Caller Trace Compass Start 888-995-2145 Revealing Trusted Lookup Intelligence
Caller Trace Compass centers on aggregating signals from credible sources to assess caller legitimacy before engagement. It cross-references dialing patterns, geolocation, and historical flags to build auditable risk profiles. The approach emphasizes data quality, provenance, and structured validation to reduce false positives. Practically, it supports evidence-driven verification and cautious engagement when legitimacy is unclear, leaving stakeholders with a clear incentive to pursue corroboration and verification steps. The implication is a framework that demands scrutiny as new signals emerge.
What Is Trusted Caller Lookup and Why It Matters
Trusted Caller Lookup refers to a system that verifies the identity of a caller before message or contact is confirmed, leveraging data from trusted sources to assess legitimacy. This framework emphasizes transparency and accountability, enabling proactive decision making. It aggregates signals for risk assessment, delivering actionable insights. In practice, trusted lookup enhances caller intelligence, supporting freedom through informed communication choices and accountability.
How 888-995-2145 Plays Into Modern Caller Intelligence
How does 888-995-2145 integrate with modern caller intelligence to refine risk assessment and decision-making? The mechanism aggregates caller intelligence from trusted lookup sources, correlating dialing patterns, geolocation, and historical flags. This synthesis supports rapid risk categorization, enhances verification steps, and informs policy decisions. The approach values accuracy over speculation, prioritizing transparent, auditable data trails.
Verifying Data Quality: Avoiding False Positives in Tracing
To maintain the integrity of caller intelligence, emphasis shifts to verifying data quality and minimizing false positives in tracing. The process emphasizes cross-checks, provenance, and consistency, filtering noise without suppressing legitimate signals.
Verifying data requires structured validation, lineage tracking, and standardized metrics. Practitioners prioritize avoiding false positives, balancing speed with accuracy to sustain reliable, freedom-respecting insights. Verifying data remains essential.
Practical Steps to Assess Legitimacy and Protect Yourself
Assessing legitimacy and safeguarding against misuse begins with a structured, evidence-based approach. The analysis emphasizes Reliable verification through cross-checks of call origin, timestamps, and metadata, complemented by independent records. Practice includes documenting discrepancies, conducting ongoing Threat assessment, and applying standardized criteria. Individuals should pause before engagement, seek corroborating sources, and deploy cautionary measures to minimize exposure while preserving informational autonomy.
Conclusion
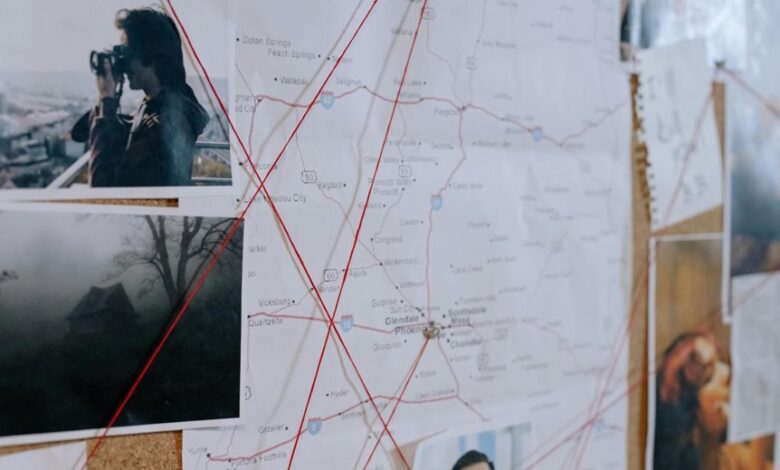
Trusted caller lookup synthesizes data from credible sources to classify engagement risk, guiding verification before interaction. By cross-referencing dialing patterns, geolocation, and historical flags, it delivers auditable intelligence that supports timely and cautious decisions. This framework emphasizes data quality, provenance, and structured validation to minimize misclassification while preserving accountability. Practically, it enables evidence-driven verification and corroboration. The process functions like a finely tuned compass, pointing toward legitimate contact while steering away from uncertain encounters.





