Phone Signal Trace Network 931-343-4484 Revealing Trusted Caller Research

Phone Signal Trace analyses aim to quantify call provenance by aggregating sender authentication data and timing signals. The approach seeks to reveal route and origin while preserving privacy, delivering a confidence metric for incoming calls. This method invites scrutiny of governance, consent, and data security. Its practical value hinges on balancing transparency with safeguards, yet unresolved questions about scalability and misuse likelihood leave a clear path for further examination. How these dynamics unfold will shape trusted communications going forward.
What Is Phone Signal Trace and Why It Matters
Phone signal trace refers to the process of identifying and recording the origin, path, and timing of a phone call or data session.
In a data-driven framework, it quantifies telecommunications behavior, enabling transparency and accountability.
The discussion centers on privacy ethics and data security, balancing individual rights with security objectives.
Objective metrics illuminate trace utility, limitations, and governance implications for freedom-minded stakeholders.
How Trusted Caller Verification Works in Practice
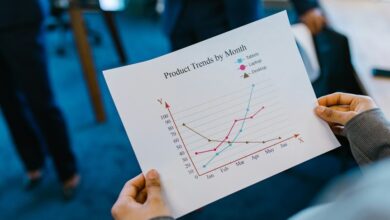
Trusted Caller Verification operates at the intersection of numeric provenance, sender authentication, and behavioral heuristics, translating signal traces into a verifiable confidence score for incoming calls. The process aggregates provenance signals, validates origin, and models caller behavior over time. Resulting trust verification outputs quantify risk, enabling system-side decisions while preserving observable patterns for analytics and continuous improvement.
Privacy, Ethics, and Legal Guardrails in Signal Tracing
Privacy, ethics, and legal guardrails in signal tracing hinge on balancing diagnostic transparency with user protections; how data provenance, consent frameworks, and compliance regimes limit collection, retention, and use shapes both trust and operational effectiveness.
The analysis emphasizes privacy ethics and legal guardrails, detailing governance, accountability, and risk controls to sustain legitimacy, minimize harm, and preserve freedom within regulated tracing practices.
Real-World Impact: Protecting Your Inbox, Calls, and Bank Details
The discussion moves from governance and risk controls to tangible outcomes, examining how signal tracing practices affect everyday communications and financial security. Analytical findings indicate improved signal integrity, reducing misrouting and spoofing incidents across inboxes and calls.
Improved caller authentication correlates with lower fraud rates, while bank details remain better shielded through verified, traceable connections and data-driven protection measures. Freedom-minded transparency underpins trust.
Conclusion
In conclusion, the study demonstrates that Phone Signal Trace networks can quantify call provenance through aggregated sender authentication data and timing signals, delivering a data-driven confidence metric for incoming communications. While promising reductions in spoofing and misrouting, the approach hinges on robust governance, consent, and stringent privacy safeguards. The analysis, mirroring a well-calibrated experiment, reveals a steady improvement in trust signals without sacrificing user privacy—a lighthouse guiding legitimate risk-aware communication in congested networks. Meticulous oversight ensures durable credibility.